QUEST INTRUST
Event Log Management Software
⇒ What is Quest InTrust Solution?
Quest InTrust is a security information and event management (SIEM) solution that provides organizations with real-time event log monitoring, analysis, and reporting capabilities. It collects and normalizes data from various sources, including Microsoft Windows and Active Directory, Unix/Linux systems, databases, and applications, to provide a unified view of an organization's security posture.
Quest InTrust offers several features such as:
- Real-time alerting: Provides real-time alerting for critical events such as failed logins, account lockouts, and policy violations.
- Threat detection: Uses advanced analytics and machine learning algorithms to detect anomalous behavior and potential threats in the network.
- Compliance reporting: Generates customizable compliance reports for various regulations such as PCI DSS, HIPAA, and GDPR.
- Forensic analysis: Allows for forensic analysis of security incidents with a detailed audit trail of user activity and system events.
- Role-based access control: Provides granular control over access to sensitive data, with role-based access control and advanced permission management.
Quest InTrust can help organizations meet their compliance requirements, detect and respond to security threats, and provide detailed reports for security audits. It's widely used in healthcare, finance, and government industries to secure their IT infrastructures.

⇒ Quest InTrust Key Capabilities
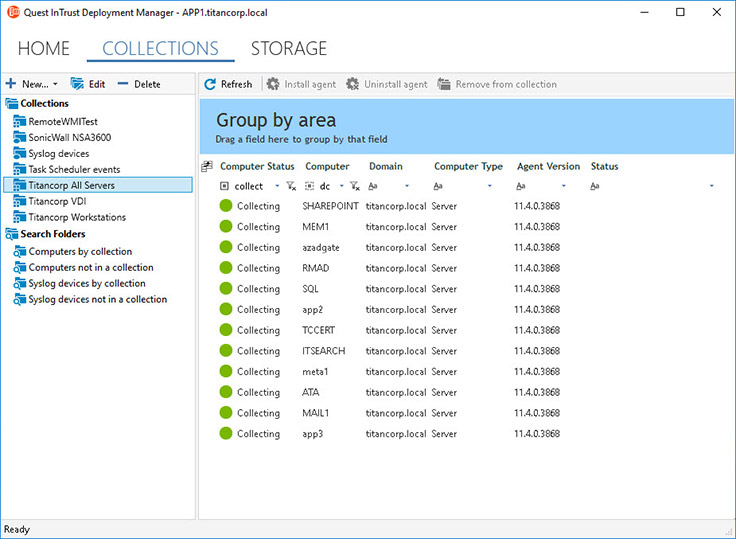
- Central log collection - Collect and store all native or third-party workstation logs from various systems, devices, and applications in one, searchable location with immediate availability for security and compliance reporting. Get a unified view of Windows event logs, UNIX/Linux, IIS and web application logs, PowerShell audit trails, endpoint protection systems, proxies and firewalls, virtualization platforms, network devices, custom text logs, as well as Quest Change Auditor events.
- Event log compression - Collect and store years of data in a highly-compressed repository, 20:1 with indexing and 40:1 without, so you can save on storage costs by up to 60%, satisfy data retention policies and ensure continuous compliance with HIPAA, SOX, PCI, FISMA and more.
- Simplified log analysis - Consolidate cryptic event logs from disparate sources into a simple, normalized format of who, what, when, where, where, and whom to help you make sense of the data. Unique, full-text indexing makes long-term event data easily searchable for fast reporting, troubleshooting, and security investigation.
- Alerting and response actions - Watch for unauthorized or suspicious user activity, such as file creation beyond threshold limits, using file extensions of known ransomware attacks, suspicious process launches, or fishy PowerShell commands. Respond to threats immediately with real-time alerts. InTrust enables you to easily trigger automated responses to suspicious events, like blocking the activity, disabling the offending user, reversing the change, and/or enabling emergency auditing.
- SIEM integration - InTrust delivers easy and reliable integration with Splunk, QRadar, ArcSight, and any other SIEM supporting common Syslog formats (RFC 5424, JSON, Snare). With InTrust’s predictable per-user license model, you can collect and store as much data as you need for as long as you want. Then use pre-built filters based on industry best practices to forward only relevant log data and alerts to your SIEM solution for real-time, security analytics. This integration enables you to slash your annual SIEM licensing costs.
⇒ Quest InTrust Additional Features
- User workstation log monitoring - Protect your workstations from modern cyberattacks, such as pass-the-hash, phishing, or ransomware, by monitoring user and administrator activity — from logons to logoffs and everything in between. Collect and store all essential details of user access, such as who acted, what that action entailed, on which server it happened, and from which workstation it originated.
- Hyper scalability - One InTrust server can process up to 60,000 events per second with 10,000 agents or more writing event logs simultaneously, giving you more efficiency, scalability, and substantial hardware cost savings. And for large, enterprise organizations who need more volume, you can simply add another InTrust server and divide the workload — scalability is virtually limitless.
- Improved insights with IT Security Search - Leverage the valuable insights from all of your Quest security and compliance solutions in one place. With IT Security Search, you can correlate data from InTrust, Change Auditor, Enterprise Reporter, Recovery Manager for AD, and Active Roles in a responsive Google-like, IT search engine for faster security incident response and forensic analysis. Easily analyze user entitlements and activity, event trends, suspicious patterns, and more with rich visualizations and event timelines.
- Automated best practice reporting - Easily convert investigations into multiple report formats, including HTML, XML, PDF, CSV, and TXT, as well as Microsoft Word, Visio, and Excel. Schedule reports and automate distribution across teams or choose from a vast library of predefined best practice reports with built-in event log expertise. With data import and consolidation workflows, you can even automatically forward a subset of data to SQL Server for further advanced analysis.
- Tamper-proof logs - Protect event log data from tampering or destruction by creating a cached location on each remote server where logs can be duplicated as they are created.
⇒ Quest InTrust Use Cases
- Compliance auditing: Quest InTrust provides comprehensive auditing capabilities to help organizations meet compliance requirements such as PCI DSS, HIPAA, and GDPR. InTrust helps monitor and track user activity on systems and applications to ensure compliance with regulatory requirements.
- Security monitoring: InTrust provides real-time alerts and reports on security events such as suspicious logins, unauthorized access attempts, and changes to sensitive data. This helps organizations detect and respond to security threats before they can cause harm.
- Troubleshooting and forensic analysis: InTrust provides detailed audit trails of changes made to critical systems and applications, helping IT teams troubleshoot issues and perform forensic analysis in case of security incidents or data breaches.
- Data governance: InTrust helps organizations monitor and audit access to sensitive data to ensure compliance with data governance policies and prevent data loss or theft.
- Infrastructure optimization: InTrust provides valuable insights into the IT infrastructure, allowing organizations to optimize their systems and applications for better performance and efficiency.
⇒ Advanced Vision IT Ltd Cybersecurity Products & Software
To build good cybersecurity protection, you need physical products and software that will help strengthen your network against attacks. If you want to view some of the ADVANCED VISION IT's cyber protection solutions, click on the links below.
- Endpoint security and antivirus software - offer a centralized management system from which security administrators can monitor, protect, and investigate vulnerabilities across all endpoints, including computers, mobile devices, servers, and connected devices. Antivirus software helps keep a computer system healthy and free of viruses and other types of malware.
- Employee Monitoring Solution - Employee monitoring solutions are software tools that enable employers to monitor the activities of their employees while they are at work. These solutions can be used to track employees' computer usage, including their internet browsing history, email communication, keystrokes, and application usage.
- Cybersecurity Backup - A backup is a copy of the system or network's data for file restoration or archival purposes. Backups are an essential part of a continuity of operations plan as they allow for data protection and recovery.
- Еmail Protection - refers to technology designed to prevent, detect and respond to cyber-attacks delivered through email. The term covers everything from gateways email systems to user behavior to related support services and security tools.
- Password Vault Manager - A password vault, password manager, or password locker is a program that stores usernames and passwords for multiple applications securely and in an encrypted format. Users can access the vault via a single “master” password.
- Vulnerability Assessment & Patch Management - The main difference between patch management and vulnerability management is that patch management is the operational process of applying remediations (patches) to vulnerable systems. Vulnerability management is the process of identifying, scanning, and prioritizing vulnerabilities for remediation.
- Data loss prevention (DLP) - makes sure that users do not send sensitive or critical information outside the corporate network.
- Microsoft Office 365 and Azure Backup and Migration - Microsoft Office 365 is a cloud-based suite of productivity and collaboration tools that includes popular applications such as Word, Excel, PowerPoint, and Outlook. Azure Backup and Migration are cloud-based services offered by Microsoft that allow organizations to protect and migrate their data to the cloud.
- Zero Trust Network Access (ZTNA) Solution - Zero Trust Network Access (ZTNA) is a security model that assumes that every user, device, and network connection is potentially insecure and should not be trusted by default. ZTNA replaces traditional perimeter-based security models, assuming that all network users and devices are trusted.
- Cloud Security - Cloud security is a collection of security measures designed to protect cloud-based infrastructure, applications, and data. These measures ensure user and device authentication, data and resource access control, and data privacy protection.
- Next-Generation Firewall - protects your network by filtering traffic and acting as a guard between your internal network and the rest of the world. Without a Firewall, your business systems could be left wide open and vulnerable to attack. It also serves as another protective layer to block malicious software.
- Active Directory Security and Recovery are critical components of any organization's cybersecurity strategy. Here are some key steps that can be taken to secure and recover Active Directory.
- SIEM & SOAR - SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) are both tools used in cybersecurity to monitor and respond to security threats.
⇒ BOUTIQUE MANAGED SERVICES
- Network domain
- Linux domain
- Microsoft domain
- Virtualization domain
- Database domain
- DevOps-as-a-Service
CONTACT OUR TEAM OF PROFESSIONALS FOR A COMPLETELY FREE CONSULTATION
CLAIM YOUR FREE IT AUDIT & CONSULTATION SCHEDULE A CALL WITH OUR TEAM