QUEST OFFICE 365 MIGRATION TOOL
⇒ Saas Management For Microsoft Office 365
- Microsoft Office 365 is a cloud-based suite of productivity tools developed by Microsoft. It includes applications like Word, Excel, PowerPoint, Outlook, OneNote, SharePoint, Teams, and many others.
- Quest is a global software provider that offers solutions for managing and securing Microsoft environments. Quest's Office 365 solution provides a set of tools that help organizations optimize their use of Office 365 and manage the migration of data and applications to the cloud.
- With Quest, you have one partner and one set of Office 365 solutions to address all your migration, management, and security needs — across Azure AD, Exchange Online, OneDrive for Business, SharePoint Online, and Teams. Whether you’re just migrating to the cloud or need help protecting all the data in it.
⇒ Office 365 Migration Solution
- Quest Office 365 tenant-to-tenant is a software solution designed to simplify the process of migrating data between two different Microsoft Office 365 tenants.
- When organizations merge or restructure, they may need to move Office 365 mailboxes, SharePoint sites, OneDrive for Business data, and other Office 365 resources from one tenant to another. Quest Office 365 tenant-to-tenant provides a reliable and efficient way to perform these migrations with minimal disruption to users.
- The solution can migrate mailboxes, calendars, contacts, and other mailbox data without requiring administrators to have high-level technical expertise. It also supports migrating Teams, SharePoint sites, OneDrive for Business data, and other Office 365 resources. The migration can be performed quickly and with minimal downtime so that users can continue to access their data during the migration process.
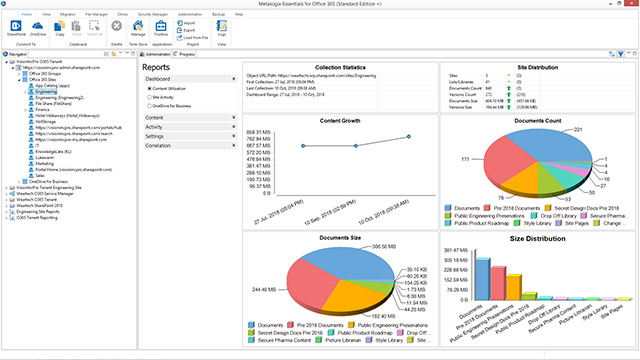
- Quest Office 365 tenant-to-tenant includes features such as pre-migration assessments, automatic mapping of user accounts, and support for incremental migrations, ensuring a smooth and efficient migration process. The solution can also provide comprehensive reporting and auditing capabilities to ensure that the migration is completed successfully. Overall, Quest Office 365 tenant-to-tenant simplifies the process of migrating Office 365 data between tenants, making it an attractive option for organizations looking to streamline their IT operations.
⇒ Office 365 Security And Protection Solution
Quest solutions help you improve your security posture and protect your data across your Office 365 and Azure AD environments to combat today’s complex threat landscape and increasingly stringent mandates.
- Backup and recovery - With Quest solutions, you can protect cloud and hybrid environments with secure backups and fast, comprehensive recovery of Azure AD and Office 365 data, including Azure AD users, groups, attributes, B2B/B2C accounts, and configurations, Exchange Online mailboxes, SharePoint Online content, OneDrive files and more.
- Auditing - Track all configuration, user, and administrator changes made in AD, Azure AD, Exchange Online, SharePoint Online, OneDrive for Business, and Teams. With On Demand Audit, you can proactively highlight security vulnerabilities and anomalous activity as well as accelerate incident investigations through responsive search and interactive data visualizations.
- Security reporting - Keep your complete Office 365 and Azure AD environment secure and compliant. Comprehensive access assessments and built-in reporting provide deep visibility into Azure resources, users, groups, permissions, and much more.
- SharePoint governance - Reduce risk, maintain compliance, and take control of who can do what in SharePoint with comprehensive policy enforcement. Automatically control access privileges and usage of SharePoint features such as versioning, file upload limits, site quotas, and site templates. Save time by delegating control to discrete site administrators or power users.
⇒ Office 365 License Management
Gain complete visibility into Office 365 licenses to achieve optimal utilization. By connecting your O365 tenant, On Demand License Management provides detailed license reports based on Microsoft APIs. These reports contain comprehensive and significant license information in an intuitive dashboard to help proactively manage license usage, license costs, and O365 productivity.
- Review how many O365 licenses are available and to whom they are assigned.
- Determine actual utilization of Office 365 services.
- Understand the cost of unutilized or under-utilized licenses and discover if a new licensing plan should be considered.
⇒ Office 365 Migration Tool Use Cases
- Migrating from legacy email platforms: The tool can be used to migrate email and other data from legacy email platforms, such as Novell GroupWise, Lotus Notes, and IMAP servers, to Office 365.
- Consolidating email platforms: The tool can help organizations consolidate their email platforms by migrating email data from multiple on-premises Exchange servers to a single Office 365 tenant.
- Upgrading to newer versions of Exchange: The tool can be used to migrate email data from older versions of Exchange, such as Exchange 2007 or Exchange 2010, to newer versions of Exchange, such as Exchange 2016 or Exchange 2019, that are hosted in Office 365.
- Merging organizations: The tool can be used to merge email data from multiple organizations into a single Office 365 tenant, allowing users to access all their email data from a single location.
- Cloud adoption: The tool can help organizations adopt cloud-based email platforms by migrating email data from on-premises Exchange servers to Office 365.
⇒ Advanced Vision IT Ltd Cybersecurity Products & Software
To build good cybersecurity protection, you need physical products and software that will help strengthen your network against attacks. If you want to view some of the ADVANCED VISION IT's cyber protection solutions, click on the links below.
- Endpoint security and antivirus software - offer a centralized management system from which security administrators can monitor, protect, and investigate vulnerabilities across all endpoints, including computers, mobile devices, servers, and connected devices. Antivirus software helps keep a computer system healthy and free of viruses and other types of malware.
- Employee Monitoring Solution - Employee monitoring solutions are software tools that enable employers to monitor the activities of their employees while they are at work. These solutions can be used to track employees' computer usage, including their internet browsing history, email communication, keystrokes, and application usage.
- Cybersecurity Backup - A backup is a copy of the system or network's data for file restoration or archival purposes. Backups are an essential part of a continuity of operations plan as they allow for data protection and recovery.
- Еmail Protection - refers to technology designed to prevent, detect and respond to cyber-attacks delivered through email. The term covers everything from gateways email systems to user behavior to related support services and security tools.
- Password Vault Manager - A password vault, password manager, or password locker is a program that stores usernames and passwords for multiple applications securely and in an encrypted format. Users can access the vault via a single “master” password.
- Vulnerability Assessment & Patch Management - The main difference between patch management and vulnerability management is that patch management is the operational process of applying remediations (patches) to vulnerable systems. Vulnerability management is the process of identifying, scanning, and prioritizing vulnerabilities for remediation.
- Data loss prevention (DLP) - makes sure that users do not send sensitive or critical information outside the corporate network.
- Microsoft Office 365 and Azure Backup and Migration - Microsoft Office 365 is a cloud-based suite of productivity and collaboration tools that includes popular applications such as Word, Excel, PowerPoint, and Outlook. Azure Backup and Migration are cloud-based services offered by Microsoft that allow organizations to protect and migrate their data to the cloud.
- Zero Trust Network Access (ZTNA) Solution - Zero Trust Network Access (ZTNA) is a security model that assumes that every user, device, and network connection is potentially insecure and should not be trusted by default. ZTNA replaces traditional perimeter-based security models, assuming that all network users and devices are trusted.
- Cloud Security - Cloud security is a collection of security measures designed to protect cloud-based infrastructure, applications, and data. These measures ensure user and device authentication, data and resource access control, and data privacy protection.
- Next-Generation Firewall - protects your network by filtering traffic and acting as a guard between your internal network and the rest of the world. Without a Firewall, your business systems could be left wide open and vulnerable to attack. It also serves as another protective layer to block malicious software.
- Active Directory Security and Recovery are critical components of any organization's cybersecurity strategy. Here are some key steps that can be taken to secure and recover Active Directory.
- SIEM & SOAR - SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) are both tools used in cybersecurity to monitor and respond to security threats.
⇒ BOUTIQUE MANAGED SERVICES
- Network domain
- Linux domain
- Microsoft domain
- Virtualization domain
- Database domain
- DevOps-as-a-Service
CONTACT OUR TEAM OF PROFESSIONALS FOR A COMPLETELY FREE CONSULTATION
CLAIM YOUR FREE IT AUDIT & CONSULTATION SCHEDULE A CALL WITH OUR TEAM