CYFIRMA PROTECT YOUR BUSINESS FROM CYBER THREATS
⇒ Who is Cyfirma and What is DeTCT?
Who is Cyfirma - Cyfirma is a cybersecurity company that specializes in providing threat intelligence and incident response services to organizations. They use a combination of proprietary technology and human expertise to gather and analyze data from various sources, such as the dark web, social media, and underground forums, to identify potential cyber threats.
What is DeTCT - is a cybersecurity threat intelligence platform offered by Cyfirma, a Singapore-based cybersecurity company. It is a cloud-based platform that uses artificial intelligence (AI) and machine learning (ML) algorithms to provide proactive and predictive threat intelligence to organizations. DeTCT stands for "Detect, Triage, Correlate, and Trigger," which are the four stages of the threat intelligence process that the platform goes through. The platform continuously monitors and analyzes data from various sources such as social media, the dark web, and other open sources to identify and prioritize emerging cyber threats. Cyfirma DeTCT provides organizations with real-time insights into emerging threats and their potential impact on their business. It also provides actionable intelligence, including indicators of compromise (IoCs) and recommendations for remediation.

⇒ What Includes DeTCT Solution?
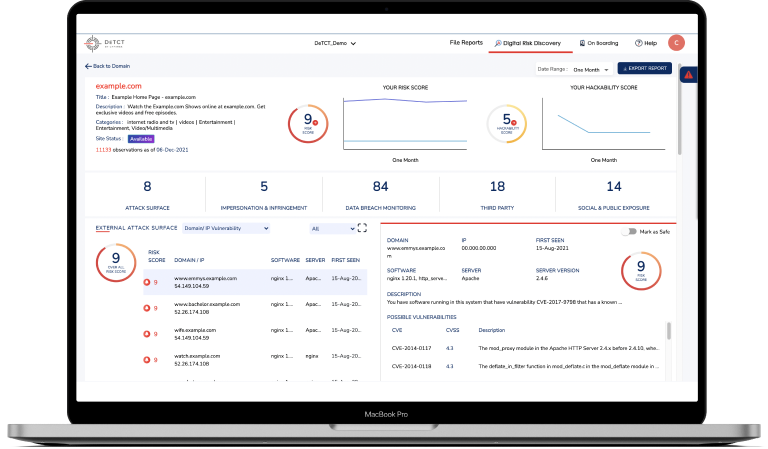
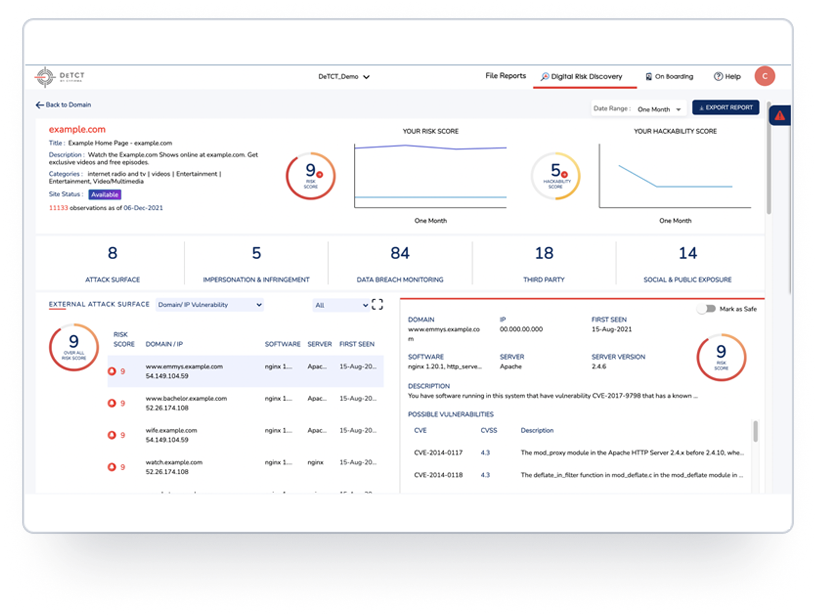
- DeTCT gives you full visibility to your digital footprint like no other - DeTCT is the only fully automated, proactive monitoring service that works 24x7 to help you stay on top of rising cyber threats.
- DeTCT gives you actionable insights so you can prioritize remedial actions - Every threat indicator comes with a risk score so you can assess its impact on your business. Recommended remedial actions are provided to help you stem data leaks and breaches. Dashboards with Risk and Hackability scores allow you to monitor progress over time.
- Attack Surface Monitoring - DeTCT monitors your attack surface so you would never be blindsided (Domain/IP Vulnerability, Certificate Weaknesses, Configuration: DNS/SMTP/HTTP, IP/Domain Reputation, Open Ports, Cloud Weakness)
- Impersonation and Infringement - DeTCT scans deep/dark/surface web and social media to look for signs of impersonation and infringement (Domain/IP Assets, Executive/People, Product/Solution, Social Handlers)
- Data Breach Monitoring - DeTCT brings to your attention data that has been stolen and is available for sale in underground marketplaces. This includes data that has been exfiltrated by ransomware groups (Emails/Identities/Credentials, Leaks, Dark Web, Phishing, Ransomware)
- Social and Public Exposures - With DeTCT, you would always know if your IP and confidential data has been exposed, including lookalike or malicious apps. You will also receive alerts on social sentiments that could present a threat to you or your business (Source Code, Confidential Files, PII/CII Dumps, Malicious Mobile Apps, Social Threats)
⇒ Cyfirma DeTCT Use Cases
- Threat Intelligence: Cyfirma DeTCT can be used to gather and analyze threat intelligence from various sources, such as dark web forums and social media platforms, to identify emerging cyber threats and provide early warnings to organizations.
- Supply Chain Risk Management: Cyfirma DeTCT can help organizations monitor the cyber risks associated with their supply chain partners and vendors. It can analyze the digital footprint of these partners to identify potential risks, such as data breaches or cyber-attacks.
- Brand Protection: Cyfirma DeTCT can help organizations protect their brand reputation by identifying online threats, such as fake social media accounts, phishing websites, and counterfeit products. It can also monitor brand mentions and sentiment on social media platforms to provide insights into customer perceptions and identify potential reputational risks.
- Cyber Threat Hunting: Cyfirma DeTCT can be used by security teams to proactively hunt for threats and identify potential vulnerabilities in their network. It can analyze network traffic, user behavior, and other indicators of compromise to identify potential threats that may have evaded traditional security measures.
- Incident Response: Cyfirma DeTCT can be used to investigate and respond to security incidents in real-time. It can provide a complete view of the threat landscape, including the tactics, techniques, and procedures (TTPs) used by attackers, to help organizations respond quickly and effectively to security incidents.
⇒ Advanced Vision IT Ltd Cybersecurity Products & Software
To build good cybersecurity protection, you need physical products and software that will help strengthen your network against attacks. If you want to view some of the ADVANCED VISION IT's cyber protection solutions, click on the links below.
- Endpoint security and antivirus software - offer a centralized management system from which security administrators can monitor, protect, and investigate vulnerabilities across all endpoints, including computers, mobile devices, servers, and connected devices. Antivirus software helps keep a computer system healthy and free of viruses and other types of malware.
- Employee Monitoring Solution - Employee monitoring solutions are software tools that enable employers to monitor the activities of their employees while they are at work. These solutions can be used to track employees' computer usage, including their internet browsing history, email communication, keystrokes, and application usage.
- Cybersecurity Backup - A backup is a copy of the system or network's data for file restoration or archival purposes. Backups are an essential part of a continuity of operations plan as they allow for data protection and recovery.
- Еmail Protection - refers to technology designed to prevent, detect and respond to cyber-attacks delivered through email. The term covers everything from gateways email systems to user behavior to related support services and security tools.
- Password Vault Manager - A password vault, password manager, or password locker is a program that stores usernames and passwords for multiple applications securely and in an encrypted format. Users can access the vault via a single “master” password.
- Vulnerability Assessment & Patch Management - The main difference between patch management and vulnerability management is that patch management is the operational process of applying remediations (patches) to vulnerable systems. Vulnerability management is the process of identifying, scanning, and prioritizing vulnerabilities for remediation.
- Data loss prevention (DLP) - makes sure that users do not send sensitive or critical information outside the corporate network.
- Microsoft Office 365 and Azure Backup and Migration - Microsoft Office 365 is a cloud-based suite of productivity and collaboration tools that includes popular applications such as Word, Excel, PowerPoint, and Outlook. Azure Backup and Migration are cloud-based services offered by Microsoft that allow organizations to protect and migrate their data to the cloud.
- Zero Trust Network Access (ZTNA) Solution - Zero Trust Network Access (ZTNA) is a security model that assumes that every user, device, and network connection is potentially insecure and should not be trusted by default. ZTNA replaces traditional perimeter-based security models, assuming that all network users and devices are trusted.
- Cloud Security - Cloud security is a collection of security measures designed to protect cloud-based infrastructure, applications, and data. These measures ensure user and device authentication, data and resource access control, and data privacy protection.
- Next-Generation Firewall - protects your network by filtering traffic and acting as a guard between your internal network and the rest of the world. Without a Firewall, your business systems could be left wide open and vulnerable to attack. It also serves as another protective layer to block malicious software.
- Active Directory Security and Recovery are critical components of any organization's cybersecurity strategy. Here are some key steps that can be taken to secure and recover Active Directory.
- SIEM & SOAR - SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) are both tools used in cybersecurity to monitor and respond to security threats.
⇒ BOUTIQUE MANAGED SERVICES
- Network domain
- Linux domain
- Microsoft domain
- Virtualization domain
- Database domain
- DevOps-as-a-Service
CONTACT OUR TEAM OF PROFESSIONALS FOR A COMPLETELY FREE CONSULTATION
CLAIM YOUR FREE IT AUDIT & CONSULTATION SCHEDULE A CALL WITH OUR TEAM