TENABLE NESSUS VULNERABILITY SCANNER
⇒ Get full visibility into your vulnerability
- Vulnerability assessment to stay one step ahead of attackers.
- Nothing in a network stays static for very long.
- Assets change, as do the vulnerabilities that can put you at risk.
- Getting a full assessment of your environment is the first step.
- Trust the #1 vulnerability assessment solution to give you peace of mind in a constantly changing security world. Trust Nessus.
- Take advantage of the industry's most trusted vulnerability assessment solution to assess the modern attack surface.
- Extend beyond your traditional IT assets secure cloud infrastructure, and gain visibility into your internet-connected attack surface.

⇒ Knowledge is power
- From the beginning, Tenable worked hand-in-hand with the security community. They continuously optimize Nessus based on community feedback to make it the most accurate and comprehensive vulnerability assessment solution in the market. 20 years later, Tenable is still laser-focused on community collaboration and product innovation to provide the most accurate and complete vulnerability data. So you don't miss critical issues which could put your organization at risk.
- Today, Nessus is trusted by tens of thousands of organizations worldwide as one of the most widely deployed security technologies on the planet - and the gold standard for vulnerability assessment.
- Eliminate attack paths by gaining the insights you need.
- Keeping pace with attackers is hard – especially with the constant barrage of new vulnerabilities and an ever-changing attack surface.
- Since 1998, Nessus has helped security teams stay a step ahead. It provides the visibility, accuracy and speed you need to protect your organization against unacceptable risk.
- Take advantage of the industry's most trusted vulnerability assessment solution to assess the modern attack surface.
⇒ Nessus benefits
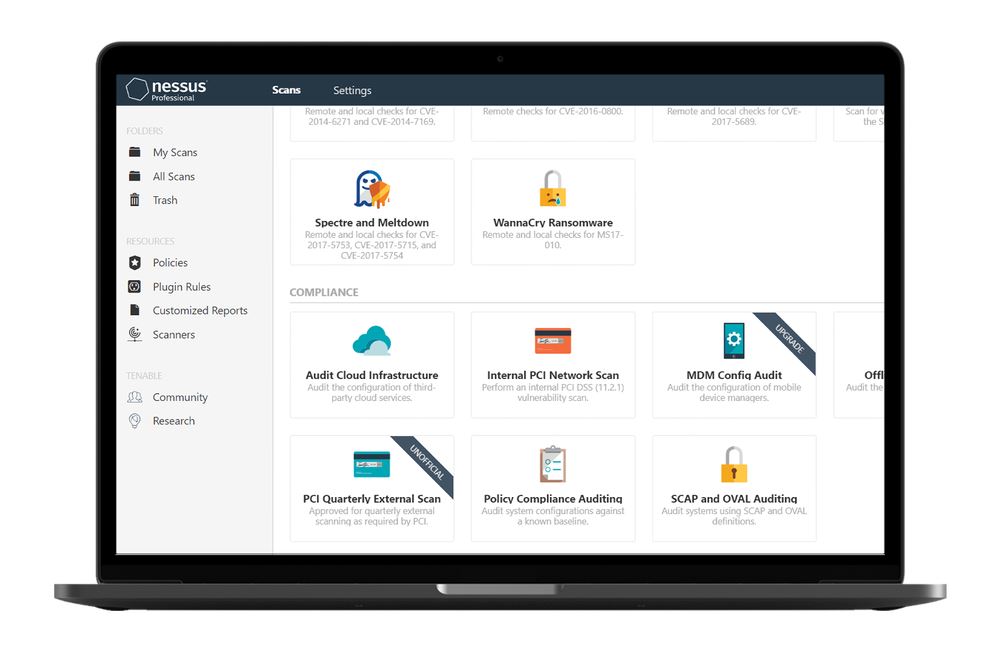
- Easy-to-Deploy, Easy-to-Use - A fully portable vulnerability assessment solution that can be deployed virtually anywhere. Policy creation is simple and only requires a few clicks to scan an entire corporate network.
- Advanced Detection Means More Protection - 65K CVEs the most in the industry. Nessus scans more technologies and uncovers more vulnerabilities than competing solutions.
- Cost Effective for Companies of All Sizes - Cost effective for any consultant or team, Nessus provides complete vulnerability scanning with unlimited assessments for one low price.
- Accurate Visibility Into Your Networks - Nessus identifies the vulnerabilities that need attention with high-speed, accurate scanning, and highlights which vulnerabilities should be addressed first.
- The Power of the Tenable Zero Day Research Team - Tenable researchers leverage extensive intel sources. Find and provide protection from the latest threats via new plugins.
⇒ Advanced Vision IT Ltd Cybersecurity Products & Software
To build good cybersecurity protection, you need physical products and software that will help strengthen your network against attacks. If you want to view some of the ADVANCED VISION IT's cyber protection solutions, click on the links below.
- Endpoint security and antivirus software - offer a centralized management system from which security administrators can monitor, protect, and investigate vulnerabilities across all endpoints, including computers, mobile devices, servers, and connected devices. Antivirus software helps keep a computer system healthy and free of viruses and other types of malware.
- Employee Monitoring Solution - Employee monitoring solutions are software tools that enable employers to monitor the activities of their employees while they are at work. These solutions can be used to track employees' computer usage, including their internet browsing history, email communication, keystrokes, and application usage.
- Cybersecurity Backup - A backup is a copy of the system or network's data for file restoration or archival purposes. Backups are an essential part of a continuity of operations plan as they allow for data protection and recovery.
- Еmail Protection - refers to technology designed to prevent, detect and respond to cyber-attacks delivered through email. The term covers everything from gateways email systems to user behavior to related support services and security tools.
- Password Vault Manager - A password vault, password manager, or password locker is a program that stores usernames and passwords for multiple applications securely and in an encrypted format. Users can access the vault via a single “master” password.
- Vulnerability Assessment & Patch Management - The main difference between patch management and vulnerability management is that patch management is the operational process of applying remediations (patches) to vulnerable systems. Vulnerability management is the process of identifying, scanning, and prioritizing vulnerabilities for remediation.
- Data loss prevention (DLP) - makes sure that users do not send sensitive or critical information outside the corporate network.
- Microsoft Office 365 and Azure Backup and Migration - Microsoft Office 365 is a cloud-based suite of productivity and collaboration tools that includes popular applications such as Word, Excel, PowerPoint, and Outlook. Azure Backup and Migration are cloud-based services offered by Microsoft that allow organizations to protect and migrate their data to the cloud.
- Zero Trust Network Access (ZTNA) Solution - Zero Trust Network Access (ZTNA) is a security model that assumes that every user, device, and network connection is potentially insecure and should not be trusted by default. ZTNA replaces traditional perimeter-based security models, assuming that all network users and devices are trusted.
- Cloud Security - Cloud security is a collection of security measures designed to protect cloud-based infrastructure, applications, and data. These measures ensure user and device authentication, data and resource access control, and data privacy protection.
- Next-Generation Firewall - protects your network by filtering traffic and acting as a guard between your internal network and the rest of the world. Without a Firewall, your business systems could be left wide open and vulnerable to attack. It also serves as another protective layer to block malicious software.
- Active Directory Security and Recovery are critical components of any organization's cybersecurity strategy. Here are some key steps that can be taken to secure and recover Active Directory.
- SIEM & SOAR - SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) are both tools used in cybersecurity to monitor and respond to security threats.
⇒ BOUTIQUE MANAGED SERVICES
- Network domain
- Linux domain
- Microsoft domain
- Virtualization domain
- Database domain
- DevOps-as-a-Service