PROOFPOINT EMAIL PROTECTION
⇒ What is a Proofpoint Email Protection
- Proofpoint Email Protection is a cloud-based email security solution that helps organizations protect their email communication from advanced threats such as phishing, malware, spam, and other email-based attacks.
- Proofpoint Email Protection offers advanced threat intelligence capabilities that help identify and block threats before they reach the end-users mailbox. It uses multiple layers of security, including sender authentication, domain-based message authentication, reporting and conformance (DMARC), and advanced URL protection to detect and block malicious emails.
- Proofpoint Email Protection also offers advanced email encryption capabilities, including policy-based encryption and secure messaging. The solution integrates with various email platforms such as Microsoft Office 365, Google Workspace, and Microsoft Exchange. It provides administrators with detailed reporting and analytics capabilities to help them identify and address email-related security risks in their organization.

⇒ Key Benefits
- See more threats, detect them faster, and protect better
- Improve productivity with fast email tracing and email hygiene
- Scale for large enterprises with complete flexibility
- Provide operational efficiencies via automation of security operations and threat response
- Extend protection with integrated email encryption, email DLP, Targeted Attack Protection, and more
- Deliver industry-leading SLAs when deployed in the cloud: - 99.999% service availability - 100% virus protection - less than one-minute email latency - 99% blocked or redirected spam
⇒ Catch Emerging Threats That Others Miss
- Detect Phishing and Impostor Email - Phishing and impostor email detection involve identifying and blocking malicious emails that are designed to trick the recipient into revealing sensitive information, such as login credentials, financial information, or personal data.
- Block Malicious and Unwanted Email - Blocking malicious and unwanted emails is important to email security.
- Track down any e-mail in seconds - Tracking down an email can depend on various factors such as the email provider, the email client used, and the specific details of the email such as the sender, recipient, and content.
- Scales for large enterprises with complete flexibility - When it comes to IT solutions, scalability and flexibility are crucial for large enterprises. These organizations require solutions that can grow and adapt to their changing needs and demands, without compromising on performance, reliability, or security.
- Raise end-user security awareness - Raising end-user security awareness is important for improving an organization's overall security posture. End-users are often the weakest link in an organization's security because they may inadvertently fall victim to phishing attacks, social engineering tactics, or other types of cyber threats.
- Centrally manage across E-mail encryption and DLP - Centrally managing email encryption and Data Loss Prevention (DLP) refers to the ability to control and monitor the security of email communication from a centralized location.
⇒ Advanced Vision IT Ltd Cybersecurity Products & Software
To build good cybersecurity protection, you need physical products and software that will help strengthen your network against attacks. If you want to view some of the ADVANCED VISION IT's cyber protection solutions, click on the links below.
- Endpoint security and antivirus software - offer a centralized management system from which security administrators can monitor, protect, and investigate vulnerabilities across all endpoints, including computers, mobile devices, servers, and connected devices. Antivirus software helps keep a computer system healthy and free of viruses and other types of malware.
- Employee Monitoring Solution - Employee monitoring solutions are software tools that enable employers to monitor the activities of their employees while they are at work. These solutions can be used to track employees' computer usage, including their internet browsing history, email communication, keystrokes, and application usage.
- Cybersecurity Backup - A backup is a copy of the system or network's data for file restoration or archival purposes. Backups are an essential part of a continuity of operations plan as they allow for data protection and recovery.
- Еmail Protection - refers to technology designed to prevent, detect and respond to cyber-attacks delivered through email. The term covers everything from gateways email systems to user behavior to related support services and security tools.
- Password Vault Manager - A password vault, password manager, or password locker is a program that stores usernames and passwords for multiple applications securely and in an encrypted format. Users can access the vault via a single “master” password.
- Vulnerability Assessment & Patch Management - The main difference between patch management and vulnerability management is that patch management is the operational process of applying remediations (patches) to vulnerable systems. Vulnerability management is the process of identifying, scanning, and prioritizing vulnerabilities for remediation.
- Data loss prevention (DLP) - makes sure that users do not send sensitive or critical information outside the corporate network.
- Microsoft Office 365 and Azure Backup and Migration - Microsoft Office 365 is a cloud-based suite of productivity and collaboration tools that includes popular applications such as Word, Excel, PowerPoint, and Outlook. Azure Backup and Migration are cloud-based services offered by Microsoft that allow organizations to protect and migrate their data to the cloud.
- Zero Trust Network Access (ZTNA) Solution - Zero Trust Network Access (ZTNA) is a security model that assumes that every user, device, and network connection is potentially insecure and should not be trusted by default. ZTNA replaces traditional perimeter-based security models, assuming that all network users and devices are trusted.
- Cloud Security - Cloud security is a collection of security measures designed to protect cloud-based infrastructure, applications, and data. These measures ensure user and device authentication, data and resource access control, and data privacy protection.
- Next-Generation Firewall - protects your network by filtering traffic and acting as a guard between your internal network and the rest of the world. Without a Firewall, your business systems could be left wide open and vulnerable to attack. It also serves as another protective layer to block malicious software.
- Active Directory Security and Recovery are critical components of any organization's cybersecurity strategy. Here are some key steps that can be taken to secure and recover Active Directory.
- SIEM & SOAR - SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) are both tools used in cybersecurity to monitor and respond to security threats.
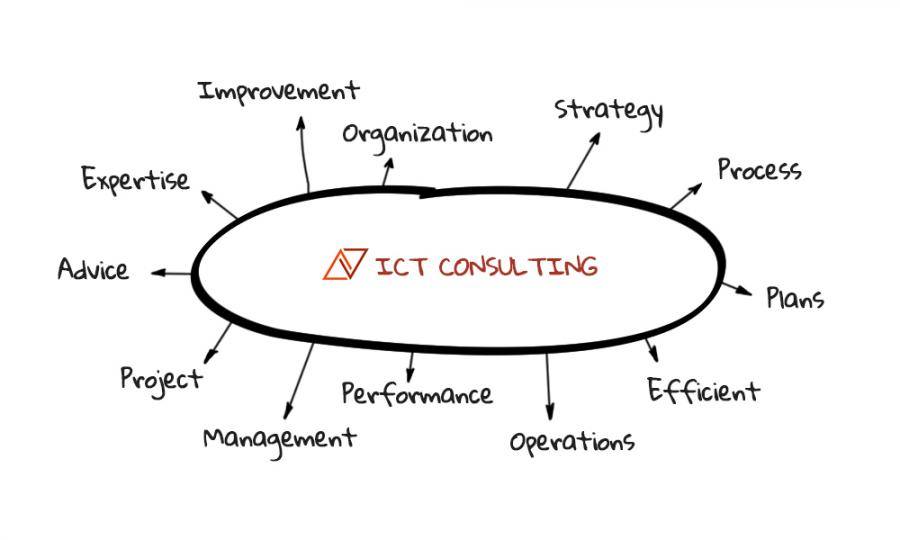
⇒ BOUTIQUE MANAGED SERVICES
- Network domain
- Linux domain
- Microsoft domain
- Virtualization domain
- Database domain
- DevOps-as-a-Service